Threats Manager Studio (TMS) enables the automatic generation of Word reports from Threat Models. This functionality is based on two different tools: TMS itself for the generation and a Microsoft Word Add-In to prepare Word templates which can be used by TMS.
The current page focuses on the preparation of the Word Templates. Please refer to Word Report, to learn how to generate reports.
For this scenario, let’s assume you already have a Word Template, in the form of a DOTX or a DOCX file. It may be a standard template provided by your organization, or something developed ad hoc. As it is, it cannot be used for automatic report generation by TMS, but it requires some preparation activities.
The first action you need to perform is to install Threats Manager Word Add-In.
After you have installed the Word Add-In, you shall open your template and add placeholders where required, using the buttons included in the Add-In itself.
For example, you may replace existing titles including the placeholders, as shown below. When you do that, you can format the placeholder itself as desired. When the report will be generated, it will inherit that format.
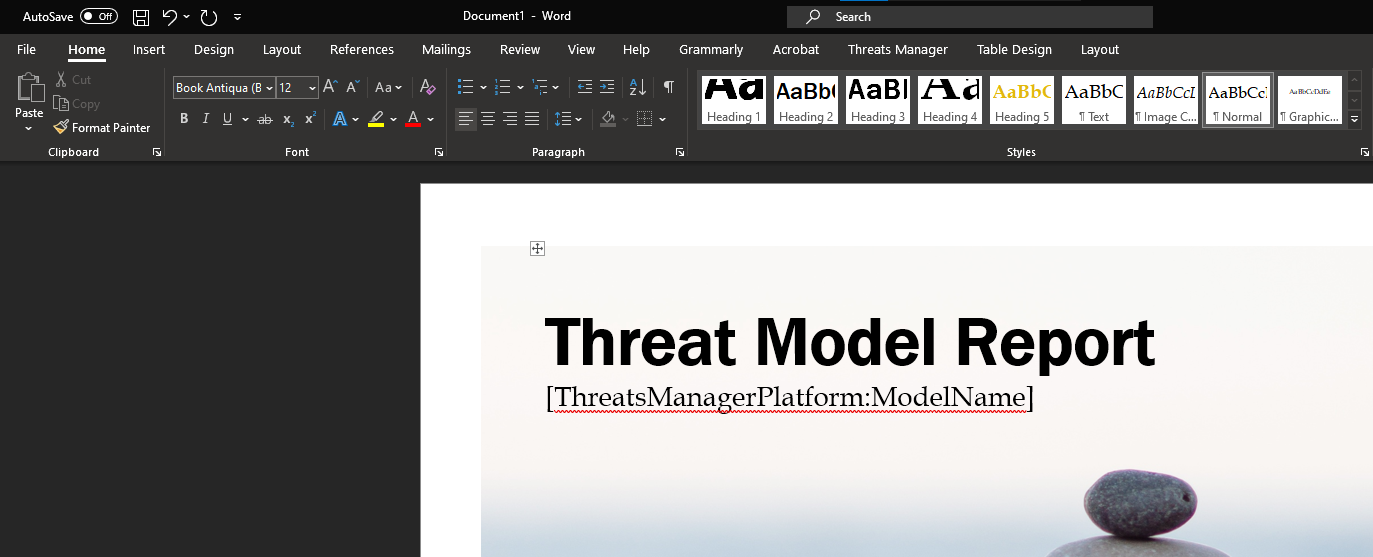
Placeholders have the following format: [ThreatsManagerPlatform:Tag], where Tag specifies the type of content to be injected. In the example above, the name of the Threat Model will be injected during the generation of the report.
Here is the list of supported placeholders.
| Section | Name | Placeholder |
|---|---|---|
| Model Properties | Insert Name | [ThreatsManagerPlatform:ModelName] |
| Insert Description | [ThreatsManagerPlatform:ModelDescription] | |
| Insert Owner | [ThreatsManagerPlatform:ModelOwner] | |
| Insert Contributors | [ThreatsManagerPlatform:ModelContributors] | |
| Insert Dependencies | [ThreatsManagerPlatform:ModelDependencies] | |
| Insert Assumptions | [ThreatsManagerPlatform:ModelAssumptions] | |
| Counters | Insert Threat Types Counter | [ThreatsManagerPlatform:CounterThreatTypes] |
| Insert Threat Events Counter | [ThreatsManagerPlatform:CounterThreatEvents] | |
| Insert Mitigations Counter | [ThreatsManagerPlatform:CounterMitigations] | |
| Insert Critical Threat Types Counter | [ThreatsManagerPlatform:CounterCriticalThreatTypes] | |
| Insert High Severity Threat Types Counter | [ThreatsManagerPlatform:CounterHighThreatTypes] | |
| Insert Medium Severity Threat Types Counter | [ThreatsManagerPlatform:CounterMediumThreatTypes] | |
| Insert Low Severity Threat Types Counter | [ThreatsManagerPlatform:CounterLowThreatTypes] | |
| Insert Info Severity Threat Types Counter | [ThreatsManagerPlatform:CounterInfoThreatTypes] | |
| Insert Proposed Mitigations Counter | [ThreatsManagerPlatform:CounterProposedMitigations] | |
| Insert Existing Mitigations Counter | [ThreatsManagerPlatform:CounterExistingMitigations] | |
| Insert Implemented Mitigations Counter | [ThreatsManagerPlatform:CounterImplementedMitigations] | |
| Insert Existing + Implemented Mitigations Counter | [ThreatsManagerPlatform:CounterExistingImplementedMitigations] | |
| Insert Approved Mitigations Counter | [ThreatsManagerPlatform:CounterApprovedMitigations] | |
| Insert Planned Mitigations Counter | [ThreatsManagerPlatform:CounterPlannedMitigations] | |
| Insert Short-Term Mitigations Counter | [ThreatsManagerPlatform:CounterShortTermMitigations] | |
| Insert Mid-Term Mitigations Counter | [ThreatsManagerPlatform:CounterMidTermMitigations] | |
| Insert Long-Term Mitigations Counter | [ThreatsManagerPlatform:CounterLongTermMitigations] | |
| Insert Not Required Mitigations Counter | [ThreatsManagerPlatform:CounterNotRequiredMitigations] | |
| Charts | Insert Threat Type Severity Chart | [ThreatsManagerPlatform:ChartThreatTypes] |
| Insert Threat Event Severity Chart | [ThreatsManagerPlatform:ChartThreatEvents] | |
| Insert Mitigation Status Chart | [ThreatsManagerPlatform:ChartMitigations] | |
| Insert Roadmap Chart | [ThreatsManagerPlatform:ChartRoadmap] | |
| Insert Short Term Projection Chart | [ThreatsManagerPlatform:ChartShortTermProjection] | |
| Insert Mid Term Projection Chart | [ThreatsManagerPlatform:ChartMidTermProjection] | |
| Insert Long Term Projection Chart | [ThreatsManagerPlatform:ChartLongTermProjection] | |
| Lists | Insert Diagrams List | [ThreatsManagerPlatform:ListDiagrams] |
| Insert External Interactor List | [ThreatsManagerPlatform:ListExternalInteractors] | |
| Insert Process List | [ThreatsManagerPlatform:ListProcesses] | |
| Insert Data Store List | [ThreatsManagerPlatform:ListStorages] | |
| Insert Flow List | [ThreatsManagerPlatform:ListFlows] | |
| Insert Trust Boundary List | [ThreatsManagerPlatform:ListTrustBoundaries] | |
| Insert Threat Event List | [ThreatsManagerPlatform:ListThreatEvents] | |
| Insert Threat Type List | [ThreatsManagerPlatform:ListThreatTypes] | |
| Insert Mitigation List | [ThreatsManagerPlatform:ListMitigations] | |
| Insert Grouped Mitigation List | [ThreatsManagerPlatform:GroupedListMitigations:Namespace#Schema#Property#Item_Style] | |
| Insert Grouped Top Mitigation List | [ThreatsManagerPlatform:GroupedListTopMitigations:Namespace#Schema#Property#Item_Style] | |
| Insert Item Template List | [ThreatsManagerPlatform:ListItemTemplates] | |
| Insert Item Template Name List | [ThreatsManagerPlatform:ListItemTemplateNames] | |
| Insert Short Term Mitigation List | [ThreatsManagerPlatform:ListShortTermMitigations] | |
| Insert Mid Term Mitigation List | [ThreatsManagerPlatform:ListMidTermMitigations] | |
| Insert Long Term Mitigation List | [ThreatsManagerPlatform:ListLongTermMitigations] | |
| Insert Short Term Mitigation List (no context) | [ThreatsManagerPlatform:ListShortTermMitigationsNoThreats] | |
| Insert Mid Term Mitigation List (no context) | [ThreatsManagerPlatform:ListMidTermMitigationsNoThreats] | |
| Insert Long Term Mitigation List (no context) | [ThreatsManagerPlatform:ListLongTermMitigationsNoThreats] | |
| Tables | Insert Threat Types Summary | [ThreatsManagerPlatform:TableSummaryThreatTypes] |
| Insert Mitigations Summary | [ThreatsManagerPlatform:TableSummaryMitigations] | |
| Insert Threat Events Summary | [ThreatsManagerPlatform:TableSummaryThreatEvents] | |
| Insert Severities | [ThreatsManagerPlatform:TableSeverities] | |
| Insert Threat Actors | [ThreatsManagerPlatform:TableThreatActors] | |
| Insert Strengths | [ThreatsManagerPlatform:TableStrengths] | |
| Insert Control Types | [ThreatsManagerPlatform:TableControlTypes] | |
| Insert Mitigation States | [ThreatsManagerPlatform:TableMitigationStatus] | |
| Insert Roadmap | [ThreatsManagerPlatform:TableRoadmap] |
Tips & Tricks
It is not necessary to install and use the Microsoft Word Add-In to add the placeholders. In fact, you can use directly the table above.
To get the best results, you should follow those rules of thumb:
- Model Properties and Counters can be applied everywhere.
- Charts and Tables can be applied in a blank row, on a dedicated paragraph.
- Lists are to be applied to a Heading: the name of each item will be assigned that style, while the body will get the Normal style. There are some exceptions to this rule: for example, the name of Diagrams is used for their Caption.
When you have prepared your template with placeholders, it is recommended to save it as DOTX, to allow using it to generate Reference Word files for Threat Models.