| Pioneer | Visible |
| Expert | Visible |
| Simplified | Hidden |
| Management | Hidden |
| Business | Hidden |
Threats Manager Studio (TMS) supports the creation of knowledgebases, to simplify the execution of Threat Models by less expert operators, and to provide a more efficient and effective experience to everyone. Those knowledgebases are called Templates.
Templates contain information on the structure of the Threat Model, but not specific data: this means that you can find Threat Types, Standard Mitigations, and Item Templates, along with metadata, but not Diagrams, Entities, Threat Events or Threat Event Mitigations.
TMS implements an approach for creating Threat Models by composition, that is from multiple Templates, which can be loaded at any time. This is fundamentally different from the experience common to other tools, which instead starts from a Template and, if a different Template is required, forces the user to start over.
Due to this approach, Templates can be focused on a specific topic, like Azure AI+Machine Learning or AWS Analytics. Therefore, they require much simpler maintenance.
Templates can be built only when the Execution Mode is Pioneer or Expert, and at least Simplified is required to consume the Templates. The current page focuses on Templates creation. Please refer to Templates Consumption for details on how to consume existing Templates.
The creation of Templates consists of exporting selected parts of the current Threat Model. For this reason, the recommended approach is to create a reference Threat Model for the scenario which is in scope for the template, starting from scratch, and then adding the specific Item Templates, then the Threat Types and Mitigations. If the Automatic Threat Generation Extension library is installed, then you should also define the Threat Generation and Mitigation Assignment rules.
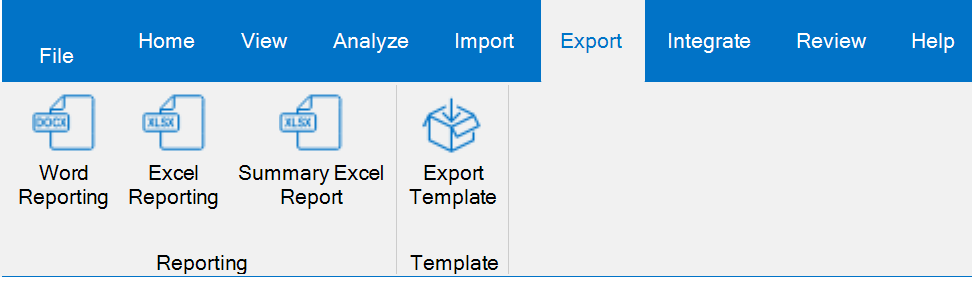
After the Threat Model is complete, you can finally export the Template by clicking the Export Template button from the Export ribbon.
This will open the Template Export Wizard.

Click Next. On the following page, you will have the possibility to edit the Name and Description for the Template, which are initially set to the values configured for the Threat Model. Click Next again.
The next page allows you to Select what to fully include.

In the example above, you can see that you can import all the different types of objects supported by the Template. If any of them would have been missing from the Threat Model, they would have been grayed out.
In this page, if a category is checked then all its items will be automatically exported. If instead an item is unchecked, then the behavior depends on the status of check box Skip granular selection of unchecked categories. For example, if this flag is checked but for example Item Templates is not, then no Item Template would be exported. If instead this flag is unchecked, then the next page would allow to select the Item Templates to export, one by one. There is a partial exception to this rule, which is represented by Property Schemas and Mitigations: in fact they are automatically exported even if not selected, if there is some dependency.
Tips & Tricks
The previous description may seem a little too complicated, but the situation is simpler than it looks: in fact, the recommended approach is to accept all defaults. This allows to export a Template in a few seconds.
When you are satisfied, click Next. In the next page you will have to select where to create the Template. Click Next, then click Finish.
IMPORTANT
When you import two Template having overlapping content, TMS handles this automatically by merging the objects that are already present. The ID of the object is used as key to understand if an object is already present. Existing values are not overwritten, though, to safeguard the work of the user. Aggregations like the relationship between Threat Events or Threat Types and Mitigations are handled by adding the missing objects.
The approach provides a reasonable support for now, but it is not perfect. For instance, if a Threat Type is present in two different Templates, and it has different Automatic Threat Generation and Mitigation Assignment rules, then those rules are not merged: those defined in the latter Template to be loaded would be lost. Improvements to this feature have been prioritized.