Threats Manager Studio (TMS) is a Threat Modeling tool that provides superior efficiency and effectiveness. But how can you practically use it to create your own Threat Models? How can you use TMS to draw diagrams that can be used to evaluate and improve the security of your solutions?
This article belongs to a short series to answer those questions, by showing the Threat Model process we currently use ourselves.
Threat Modeling with TMS is not much different than other tools, at least at the very start of the experience. In fact, you still have to analyze the system using the Threat Modeling approach, to understand it. This is an important topic, and a specific post will cover it soon.
Let’s assume that you have already discussed the solution with its Owners and Architects. If you need to learn more about this process, please get a look at the last post in the series: Threat Modeling with TMS: the Interviews. Now, you have a good understanding of the system. It’s time to move to TMS!
Details of your Threat Model
The first activity you need to do is to specify the details of your Threat Model. This can be done using the Threat Model Properties button in the Home ribbon.

This tool shows an Item Editor for the whole Threat Model. It allows to specify the Name of the Threat Model, its Description, the Owner which would be the main Threat Modeler, and the Contributors.

The Threat Model Properties tool allows also to specify the Assumptions. Please take great care to add in this field all aspects that may be controversial and that are significant to attest the correctness of the Threat Model. For instance, if you have a Cloud solution, you cannot Threat Model all of it: you will have at least to leave out the Services provided by the Cloud Provider, for the part that is its responsibility. In fact, you do not have the resource, time and information required to include in your study a Threat Model of the Cloud Services, therefore you need to trust the Cloud Provider to have designed and built them securely. Another example is related to unknowns: for instance, if your solution relies on an Identity Provider (IdP) which is managed and maintained by a specialized structure within the IT, then you can assume that this IdP is managed securely. The idea is that if it is not, you may have additional risks and therefore you need to track the assumption.
It is important to note that the Assumptions section is subject to be revised and integrated more times during the preparation of the Threat Model. When you see something critical you need to take note of, remember to write it down here.
Finally, you may want to specify the technical Dependencies of your solution.
The Templates
Having done the bureaucratic part of the would want to do is to identify one or more Template you need, to compose the knowledgebase specific for your solution. When you start TMS, it provides you a Threat Model that is empty. In fact, the Threat Model initially misses any Diagram or Entities, and also any Threat Type or Mitigation. Moreover, TMS initially provides only basic Entities. To address this situation, you need to provide TMS with the knowledge related to your specific problem space, by importing Templates.
In a nutshell, Templates are stripped-down Threat Models. They include Threat Types, Mitigations, Item Templates, Property Schemas and a few other pieces of information. They miss objects like Diagrams, Entities and Threat Events which are typically part of the Threat Model. You can consider them as highly-specialized knowledgebases, and you can combine them to create your specific context. This site publishes a growing collection of Templates. You can download and use any of them for free in your Threat Models. For now there is only a Template published, but others will join it soon enough. You can even contribute to the collection with your own Templates, using the Template Upload page.
The Auto Threat Gen Extension library
A lot of Templates define rules to generate automatically Threat Events and associate Mitigations, based on the diagram. This functionality is not present by default in TMS. In fact, TMS has been designed to provide as few functionalities as it is possible, to be extended as needed. Automatic Threat Generation may be considered a very common need, but not everyone would require it or that specific approach. For example, in the hopefully near future someone may create an Extension implementing AI-based Threat generation. What happens if you load a Template that uses some functionality provided by an Extension? You get a warning, but TMS still imports the Template successfully, removing the information associated to the missing Extension. For example, if you load a Template supporting Automatic Threat Generation on a TMS missing that Extension, you will not be able to generate Threats or associate Mitigations. You will not be able to fix this at a later stage, for example by loading the Extension.
The above behavior may represent a problem for some scenarios, and will be addressed soon.
Use this moment to go to the Analyze ribbon and check if the Generate Threat Events & Mitigations button is present. In that case, close TMS, then go to Downloads page to install the Auto Threat Gen Extension library. Restart TMS and then continue from the next step.

Importing Templates
Now we can start importing the required templates. Let’s assume in our case that you have a simple solution based on some core services offered as part of Azure PaaS. You are lucky! There is already a Template exactly for that scenario. So download it using the Download Template link: you will get a file with extension .TMT. You cannot open those files directly: you have to import them. So go to the Import ribbon and click the Import Template button. TMS will ask you to select the template file you want to import. Pick the one you have just downloaded, and then accept all defaults. The procedure is described in Templates.

Now you can go to the Threat Type List, to the Known Mitigation List or to the Item Template List and check that indeed they are not empty anymore.
Drawing the Diagram
It’s finally time to start drawing your Threat Model. To do that, you can follow a simple process of dragging and dropping the various stencils to the Drawing Pane, from one of the Palettes placed in the left of the screen. There are four of them:
- The Basic Objects palette, which is immediately visible when you open a Diagram.
- The Item Templates palette, which contains the type of entities defined in the imported Templates.
- The Existing Objects palette, which shows entities included in other Diagrams and missing in the current one.
- The Threat Types palette, allows assigning Threat Types to Entities and Flows by simply dragging and dropping them where they are required.
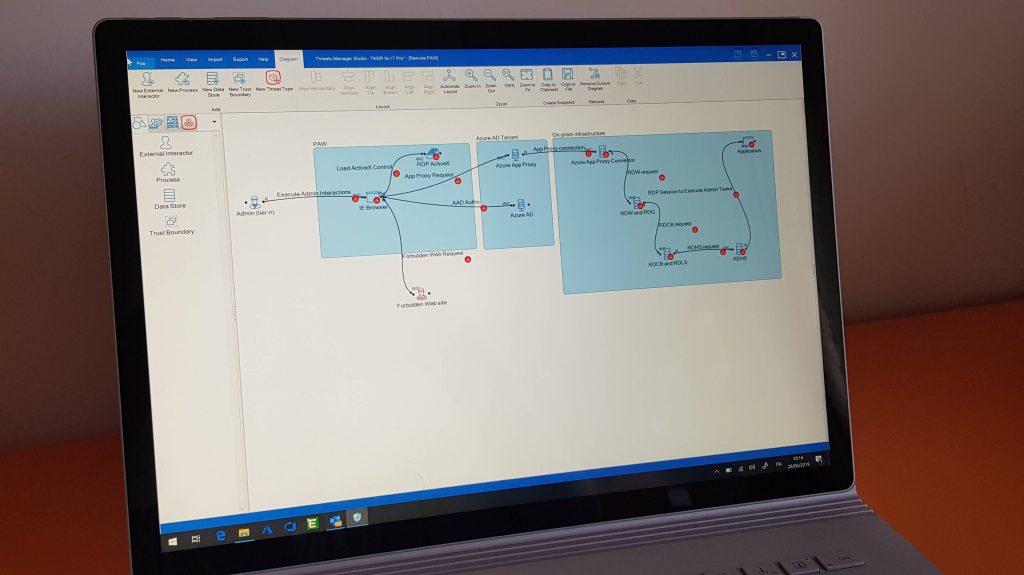
As a result, you would be able to draw a diagram like the one shown below.

It is important to note that creating a single diagram would not be enough in most situations. It may be too simplistic and require to go more in depth to get significant details about the solution and its risks. The solution may require to drill down some components like the Web API and misses internal Trust Boundaries. For example, what if this is not a simple Web API, but something exposing a microservices architecture? Most importantly, it does not consider important scenarios, like Operation and the CI/CD processes. For our purposes, it may be still a good starting point.
Missing Item Templates
During the creation of the Diagram, you may need to add an Entity of a type that is not included in the knowledgebase. What to do, then? There are two possible scenarios: another template may define the missing Entity, or you may need to create it from scratch.
If some Template already defines that Entity, you can simply import the said Template. You can do that at any time, and you can even import only selected part of the Template. If you have already created the object, you can convert it to the required Item Template using command Change Template from the context menu of the target object.
If instead there is no Template defining the required Item Template, you create it yourself, by using command Derive Template from the context menu of the target object.
Next Steps
Now that you have your diagram done, you can move to the Threat Event identification and Mitigation assignment phase. This is the topic of the next post.
Leave a Reply